Understanding AES Encryption: A Deep Technical Dive

The Advanced Encryption Standard (AES), established by the U.S. National Institute of Standards and Technology (NIST) in 2001, is a symmetric block cipher chosen to protect classified information. Let's explore the mathematically elegant mechanics of how it secures the digital world—from WhatsApp messages to banking infrastructure.
1. Symmetric Key Cryptography Foundation
AES relies on symmetric key cryptography. This means the identical key used to encrypt the plaintext is strictly required to decrypt the ciphertext. Unlike asymmetric cryptography (such as RSA or Elliptic Curve), which involves computationally expensive public-private key pairs, symmetric algorithms are exceptionally fast. This speed makes AES the industry standard for bulk data encryption, operating seamlessly within protocols like TLS/SSL and disk encryption software.
Depending on the security requirements, AES operates with three key lengths: 128-bit, 192-bit, or 256-bit. The larger the key, the exponentially higher the number of possible combinations ($2^256$ for AES-256), making brute-force attacks physically impossible given current computational limits.
2. Under the Hood: The State and the Rounds
AES doesn't encrypt data linearly. Instead, it operates on a fixed-size 128-bit block of data at a time. This block is organized into a 4x4 matrix of bytes known as the state.
The algorithm puts this state through multiple rounds of transformations. The number of rounds depends directly on the key length:
- AES-128: 10 Rounds
- AES-192: 12 Rounds
- AES-256: 14 Rounds
Except for the final round (which omits the MixColumns step), each round consistently executes four specific mathematical operations: SubBytes, ShiftRows, MixColumns, and AddRoundKey.
Phase 1: SubBytes (Confusion)
The SubBytes step is a non-linear substitution. Every single byte in the 4x4 state matrix is substituted with another byte using a predefined lookup table known as the Rijndael S-box.
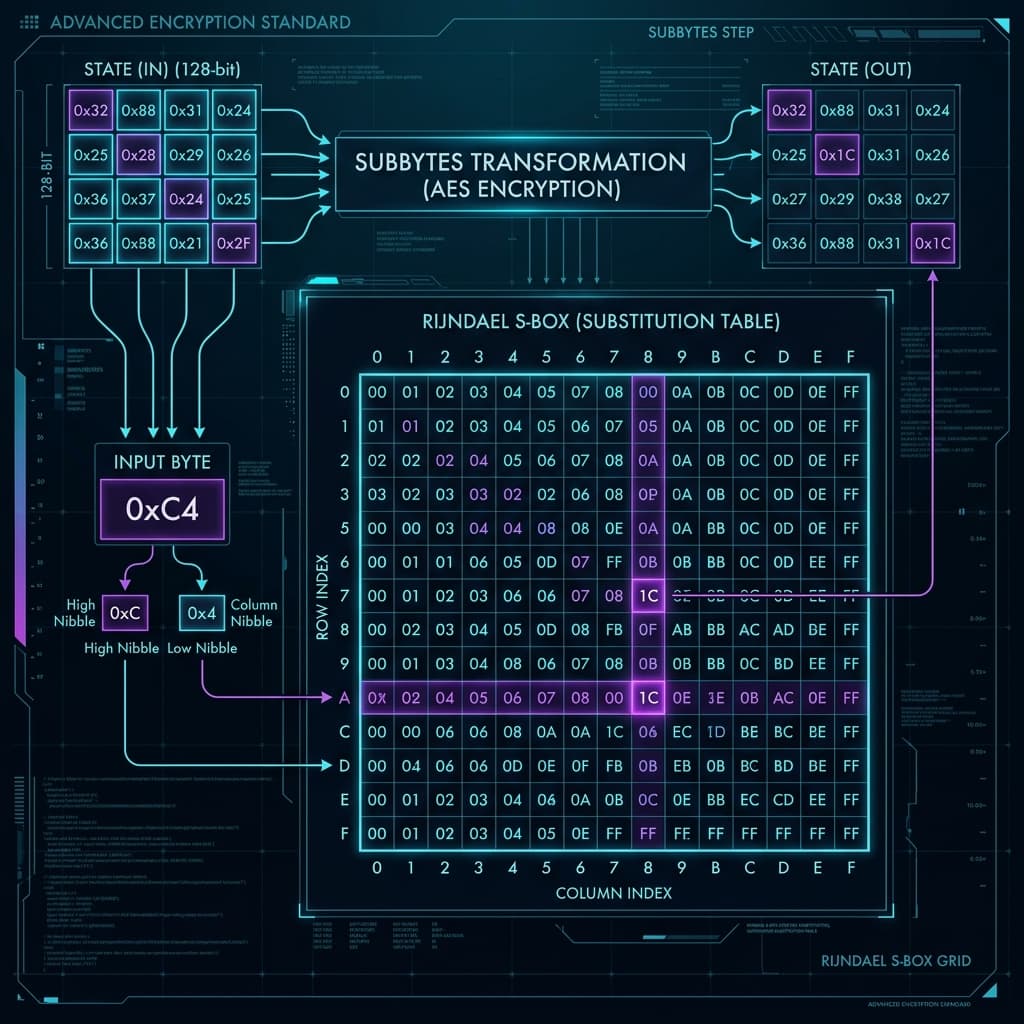
This substitution is purposefully designed to thwart algebraic attacks. By replacing values non-linearly, AES introduces confusion—a cryptographic property coined by Claude Shannon, which dictates that the relationship between the encryption key and the ciphertext should be as complex and opaque as possible.
Phase 2: ShiftRows (Diffusion)
While SubBytes operates on individual bytes, ShiftRows operates on the rows of the state matrix. It is a simple transposition step:
- Row 0: Not shifted.
- Row 1: Shifted cyclically to the left by 1 byte.
- Row 2: Shifted cyclically to the left by 2 bytes.
- Row 3: Shifted cyclically to the left by 3 bytes.
This guarantees that the columns are mixed. Without ShiftRows, each column in the state matrix would be encrypted independently, drastically weakening the cipher.
Phase 3: MixColumns (Diffusion)
MixColumns provides extreme diffusion—meaning that changing a single bit of plaintext affects a vast number of bits in the ciphertext.
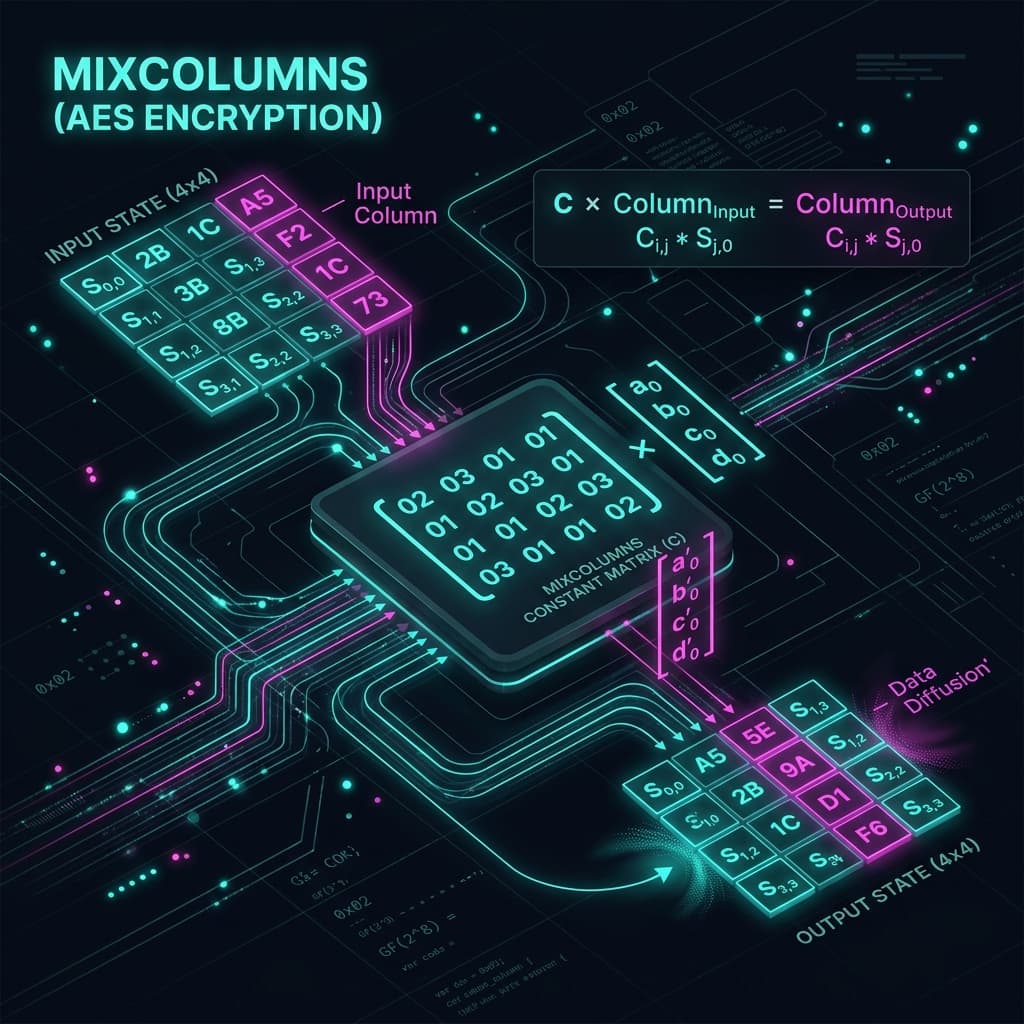
In this step, each column of the state matrix is treated as a four-term polynomial. The column is multiplied by a fixed constant polynomial matrix over the finite field Galois Field $GF(2^8)$. Because of the mathematical properties of this multiplication, the output of any given byte relies on the input of all four bytes in that column.
Note: The final round of AES explicitly skips the MixColumns step to ensure the encryption and decryption processes remain perfectly invertible without adding unnecessary computational overhead.
Phase 4: AddRoundKey
Finally, the AddRoundKeystep brings the secret key into play. A "Round Key" is derived from the main encryption key via the AES Key Schedule algorithm. This round key is seamlessly combined with the state matrix using a bitwise XOR (Exclusive OR) operation.
Because XOR is perfectly invertible, decryption is as simple as XORing the ciphertext with the same round key again.
3. Hardware Acceleration & Performance
Because AES is so ubiquitous, modern CPUs from Intel, AMD, and ARM come equipped with dedicated AES-NI (New Instructions). By implementing the algorithm directly onto the silicon hardware, processors can execute AES encryption and decryption at gigabytes per second, using minimal power.
Conclusion
The architectural brilliance of AES lies in its elegant simplicity and mathematical rigor. The continuous loops of diffusion (via ShiftRows and MixColumns) combined with non-linear confusion (via SubBytes) ensure that after just a few rounds, the ciphertext appears entirely random. When implemented correctly with secure block modes (like GCM), AES remains unbreakable by any known practical attack, solidifying its place as the bedrock of modern digital security.